Requirements:-
- You must have a webhost like fileave.com, 110Mb.com, etc.
- The file you want to spread must be FUD.
- If not then download Stealth Crypter (100 % FUD) from GOOGLE
Follow the Given Steps:-
1. We are now going to setup our Facebook app.
2. You will need a Facebook account to register a Facebook app.
3. For That Go To http://www.facebook.com/developers/createapp.php
4. Now on Further on right Corner you will see a link named as Setup New Application.
5. Now fill in the name you want for your application Example I Write "GirlFriend".
6. Now Click on I agree Terms and then Click on Create Application.
7. Now Fill the Following Details and then click on Save Changes.
8. Now click on 'Facebook Integration'.
9. On this page the only thing you need to fill in is the 'Canvas Page'.
10. This allows you to use a Facebook URL for your like button.
11. Fill it in with a name regarding your Facebook page, it can't already be taken For Example I write: ‘lovegirlfriends’.
12. Then click save changes.
10. This allows you to use a Facebook URL for your like button.
11. Fill it in with a name regarding your Facebook page, it can't already be taken For Example I write: ‘lovegirlfriends’.
12. Then click save changes.
13. Now Create Your Like Button.
14. Now further going to create a like button to help spread Your App,Go to this link: http://developers.facebook.com/docs/reference/plugins/like
14. Now further going to create a like button to help spread Your App,Go to this link: http://developers.facebook.com/docs/reference/plugins/like
15. The only bit you need to fill in is the URL of the page about the canvas so it will be 'http://apps.facebook.com/lovegirlfriends/'
16. Now Further Click on 'Get Code' and copy the IFRAME code to notepad or something so you can use it later.
16. Now Further Click on 'Get Code' and copy the IFRAME code to notepad or something so you can use it later.
17. Now Next Step is editing your 'index.html'. We now need to edit our html file so open it in anything that you can edit it with, notepad if you have to.
18. At this stage you must have your file that you want to spread uploaded to your web host, it cannot be a site such as megaupload it must be a direct link ending in “.exe”.
19. Now upload your Virus/Stealer/Rat in any Webhost
20. The better webhost for server is fileave.com And it will generate the link look like:-'http://apajrlab.fileave.com/apajr.exe'
19. Now upload your Virus/Stealer/Rat in any Webhost
20. The better webhost for server is fileave.com And it will generate the link look like:-'http://apajrlab.fileave.com/apajr.exe'
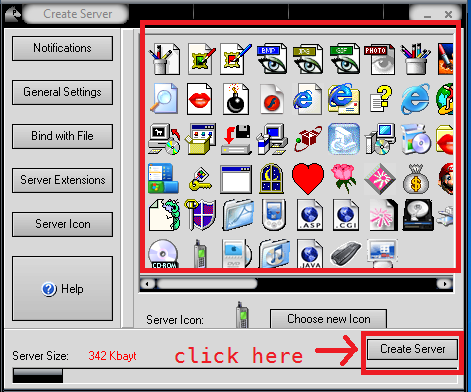
21. Now open index.html File and it will look like:- Look for Code:value="ENTER THE URL FOR YOUR VIRUS"
23. Next look for Code:'REPLACE THIS TEXT WITH YOUR FB LIKE BUTTON'
25. Upload Your Files on your webhost I follow fileave.com or 110Mb.com
26. This is the easy part; now just upload your three files to your web host.
27. First create a Directory named as Facebook and then upload the three files.
28. Editing Your App
a. Now we need to edit your app to display the content of the files you just uploaded.
b. Now get us back to allow us to edit the canvas settings.
c. Navigate to the page we were on before and Now we’re going to fill in the canvas URL, Fill it in with the URL where the files are, it must end with a '/'. I recommended uploading your files to a sub directory. E.g. 'http://apajrlab.fileave.com/Facebook/'
29. Click save settings.
NOTE: - IF FILEAVE.COM displays Error then use this Step
If u have got any Error look like Run time Error or your Canvas URL not Saved then better solution is to upload your Files on other Host like 000webhost.com
Note: Don't create a Sub-Directory:
It looks like this:
30. If u have till got Error then goto tinyurl.com or Forward your URL to any Websiteand then write that link on Canvas Url.
31. Now Next Step is testing, To test it, try opening a new browser and visiting your app:'http://apps.facebook.com/lovegirlfriends/'
31. Now Next Step is testing, To test it, try opening a new browser and visiting your app:'http://apps.facebook.com/lovegirlfriends/'
You should see something like:
32. Click run and your file with download and execute.
33. Click the like button for it to show up on your friend’s news feeds and start spreading. (Note: Victims must have java)
33. Click the like button for it to show up on your friend’s news feeds and start spreading. (Note: Victims must have java)